SOC-200 / OSDA is OffSec’s flagship defensive certification — and the most respected SOC analyst credential in India in 2026. This guide is the no-fluff exam preparation plan our SOC trainers use with candidates at Macksofy Trainings to pass on attempt one.
If you’re a blue-team professional, SOC analyst, detection engineer, or DFIR aspirant, SOC-200 (OSDA — OffSec Defense Analyst) is worth every rupee you invest. Here’s how to pass it.
What is SOC-200 / OSDA?
SOC-200 is OffSec’s 200-level defensive course, culminating in the OSDA (OffSec Defense Analyst) certification. Launched in 2022, OSDA is positioned as OffSec’s answer to SANS GCDA and CompTIA CySA+ — a hands-on, practical defensive cert focused on detection of real adversary behaviours, not theory or memorisation.
OSDA tests whether you can:
- Detect and analyse active attacks in a monitored environment
- Correlate logs across endpoint, network, and identity telemetry
- Understand and trace attacker TTPs mapped to MITRE ATT&CK
- Write clear, actionable detection narratives
Exam format (2026)
- Duration: 23 hours 45 minutes of active exam + 24 hours for report
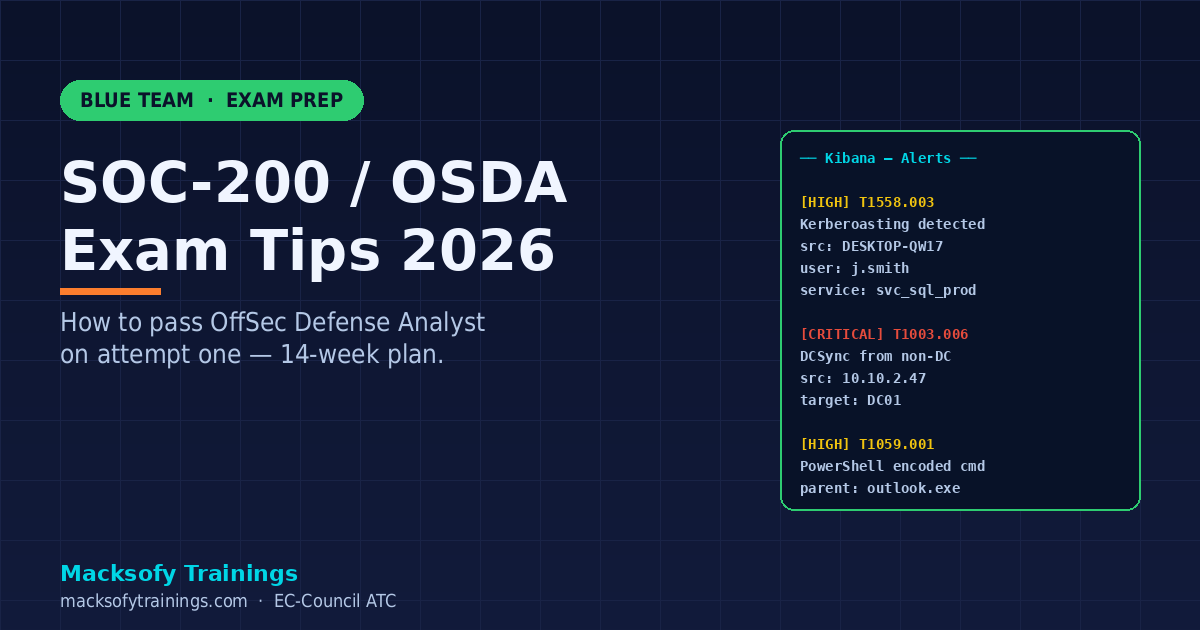
- Environment: proctored Virtual Environment with SIEM (Elastic/Kibana), Windows endpoints, AD domain
- Goal: detect and document 8 attack chains / phases
- Pass: Documenting at least 7 of 10 detection points
- Report: professional-quality timeline + technical analysis + recommendations
- Cost: ~$1,649 USD Learn One bundle (similar to OSCP). Exam retake ~$249
Syllabus — what you must master
- MITRE ATT&CK framework (Initial Access, Execution, Persistence, Privilege Escalation, Defense Evasion, Credential Access, Discovery, Lateral Movement, Collection, C2, Exfiltration, Impact)
- Windows endpoint telemetry — Security event log, Sysmon, PowerShell logging
- Linux auditd and syslog-level detection
- Web server logs — Apache/Nginx/IIS access + error correlation
- Active Directory attack detection — Kerberoasting, AS-REP, DCSync, Golden Ticket
- Network-level detection — Zeek/Suricata, DNS tunnelling, C2 beaconing
- Email-based threats — phishing detection, attachment analysis
- Malware IOCs — process trees, file writes, registry, network indicators
- SIEM query language — KQL in Elastic, Splunk SPL fundamentals
- Detection writing — rules, thresholds, tuning
Prep plan — 12-16 weeks
This is the schedule we give our candidates:
Weeks 1-4: Foundations
- MITRE ATT&CK matrix — memorise T1xxx IDs for all Initial Access and Execution techniques
- Sysmon — install on a lab Windows VM, run every event ID 1-30 intentionally
- Read @13Cubed’s Sysmon primer series + SwiftOnSecurity’s config
- Elastic / Kibana basics — ingest sample logs, build basic dashboards
Weeks 5-8: OffSec labs
- Work through every OSDA lab module sequentially — do not skip
- For each attack: reproduce it in your own lab, then detect it with raw logs
- Build a personal “detection notebook” — Markdown with one page per technique, attacker command + log signature + query
Weeks 9-12: Practice + reporting
- TryHackMe SOC Level 1 + Level 2 paths (2026 tracks updated for Entra ID scenarios)
- Blue Team Labs Online — “Investigation” challenges map closely to OSDA attack chains
- LetsDefend SOC Analyst path — writing investigation reports in LetsDefend’s format is excellent OSDA exam practice
- Write 3-5 mock reports from scratch, timing yourself to 8 hours each
Weeks 13-14: Mock exams
- Do at least one full 48-hour mock: 23h45m lab + 24h report window
- Have a senior analyst review your report — structure matters more than content depth
Tools you must be fluent with
| Category | Tools |
|---|---|
| SIEM | Elastic/Kibana, Splunk, Microsoft Sentinel (bonus) |
| Endpoint | Sysmon, Windows Event Viewer, PowerShell transcription |
| Network | Wireshark, Zeek, Suricata, tcpdump |
| Malware analysis | PE-bear, CFF Explorer, Process Hacker, REMnux basics |
| Query languages | KQL, SPL, Lucene query syntax |
| IOC hunting | YARA, Sigma rules, Snort/Suricata signatures |
| Frameworks | MITRE ATT&CK, Sigma HQ, Atomic Red Team |
Exam day tips
- Take the first hour to survey the environment — inventory VMs, SIEM indices, log sources, time range of attacks
- Build a running timeline from hour zero — spreadsheet with timestamp, host, technique, evidence source
- Map every finding to MITRE ATT&CK — graders want T1xxx tags, not narrative-only notes
- Screenshot religiously — every Kibana query, every event, every grep result with timestamps visible
- Document DURING the exam, not after — fighting report fatigue later is brutal
- Use the 30-minute break — stand up, walk outside, eat protein + complex carbs. Sugar crashes kill the second half
- Don’t chase false positives forever — if you’ve spent 90 minutes on something with no reward, pivot and come back
- Report structure: Executive summary → Chronological attack narrative → Per-phase technical evidence → Recommendations. OffSec’s pass rate on reports is brutal — clean structure saves you
Common mistakes that fail candidates
- Under-practicing report writing — the exam is 50% detection and 50% documentation
- Ignoring Linux / web server logs — exams increasingly mix endpoints
- Memorising ATT&CK without hands-on reproduction — you’ll fumble on novel chains
- Treating the exam like CTF flag capture — it’s an investigation narrative, not a puzzle
- Running out of time on the report because the lab was “fun” — budget exactly 50/50
OSDA vs OSCP — should I take OSDA first?
Depends on your intended career track:
- Pentest / red team career → OSCP first. OSDA optional bonus
- SOC / blue team / DFIR career → OSDA first. Adds massive credibility at SOC manager level
- Purple team / both → OSCP then OSDA within 12 months. Our CRTO vs OSCP comparison also applies: see CRTO vs OSCP Honest Comparison 2026
Average Indian OSDA-holder salary in 2026 is ₹12-18 LPA mid-career, rising to ₹22-32 LPA for SOC Lead / Senior Detection Engineer roles at BFSI and MSSPs.
OSDA vs CompTIA CySA+ vs GCDA (SANS)
- OSDA — hands-on, practical, no multiple choice. Industry growing respect.
- CompTIA CySA+ — multiple choice + performance-based. HR-friendly but less rigorous.
- GCDA (SANS) — deep and respected but ₹4+ lakh course cost.
For Indian BFSI + Big 4 SOCs in 2026, OSDA and CySA+ both open doors. For senior detection engineer / threat hunter roles, OSDA + GCDA / GCIA is the stretch combo.
FAQ
Is OSDA worth it in India?
Yes for SOC Analyst, Detection Engineer, Threat Hunter, SOC Lead, and DFIR roles. Approximately 40% of Indian BFSI and product-company SOC JDs in 2026 list OSDA or equivalent (GCDA / CySA+). The hands-on credibility is hard to fake in interviews.
Can I pass OSDA without prior OSCP-level offense skills?
Yes, but harder. OSDA presumes you understand how attacks work — prior CEH / HTB Academy / OSCP-level study makes detection intuitive. Without that, budget 3-4 extra weeks on attacker-side practice before starting OSDA labs.
Does OffSec provide the SIEM in the exam?
Yes. You get a pre-built Elastic / Kibana environment with ingest pipelines already configured. You do not need to build a SIEM from scratch — just to query it efficiently.
How does OSDA compare to the Blue Team Level 2 (BTL2)?
BTL2 from Security Blue Team is similar in spirit but the exam format differs — BTL2 is open-book 24-hour with report, no proctoring. BTL2 is cheaper (~$750). OSDA’s brand recognition is stronger in BFSI and Big 4 hiring in India.
Can I combine OSDA prep with our SOC Analyst training?
Yes — our SOC Analyst Training India 2026 programme covers the same detection fundamentals, plus EC-Council CSA prep, plus OSDA-aligned labs. Most candidates take our SOC foundation course first, then tackle OSDA independently or with mentorship.
What happens if I fail the exam?
OffSec allows one free retake if you purchase within 30 days, at a discounted rate for up to a year. Review the report — OffSec feedback is brutal but accurate — and retake with 6-8 weeks of focused weak-area practice.
Ready to commit?
Our SOC Analyst Training programme has placed 200+ analysts into SOC roles at Indian BFSI, MSSPs, and product companies since 2021. Combined with OSDA certification, graduates average ₹8-14 LPA starting. Contact Macksofy for next Mumbai / Pune / Hyderabad batch dates.